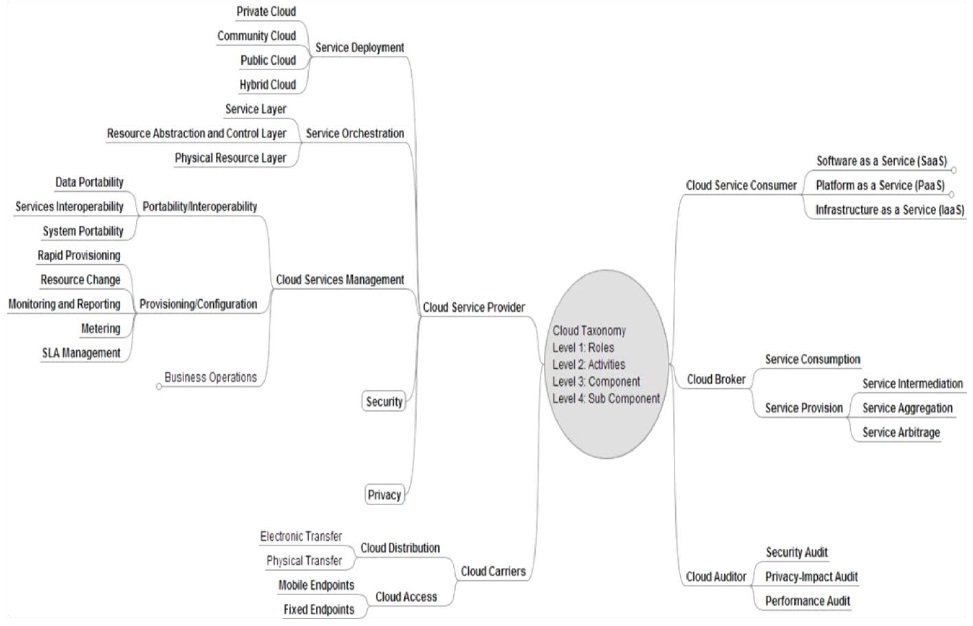
To demystify the ambiguity surrounding cloud services the nist cloud computing services public working group analyzed the nist cloud computing definition and developed guidance on how to use it to evaluate cloud services.
Nist cloud security 2017.
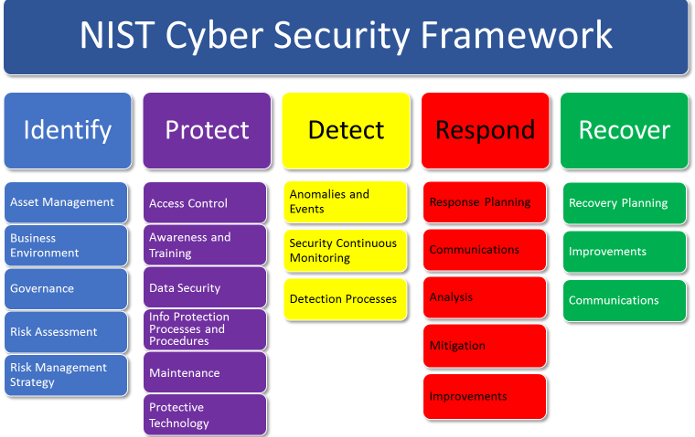
This paper presents a methodology allowing for cloud security automation and demonstrates how a cloud environment can be automatically configured to implement a set of nist sp 800 53 security controls.
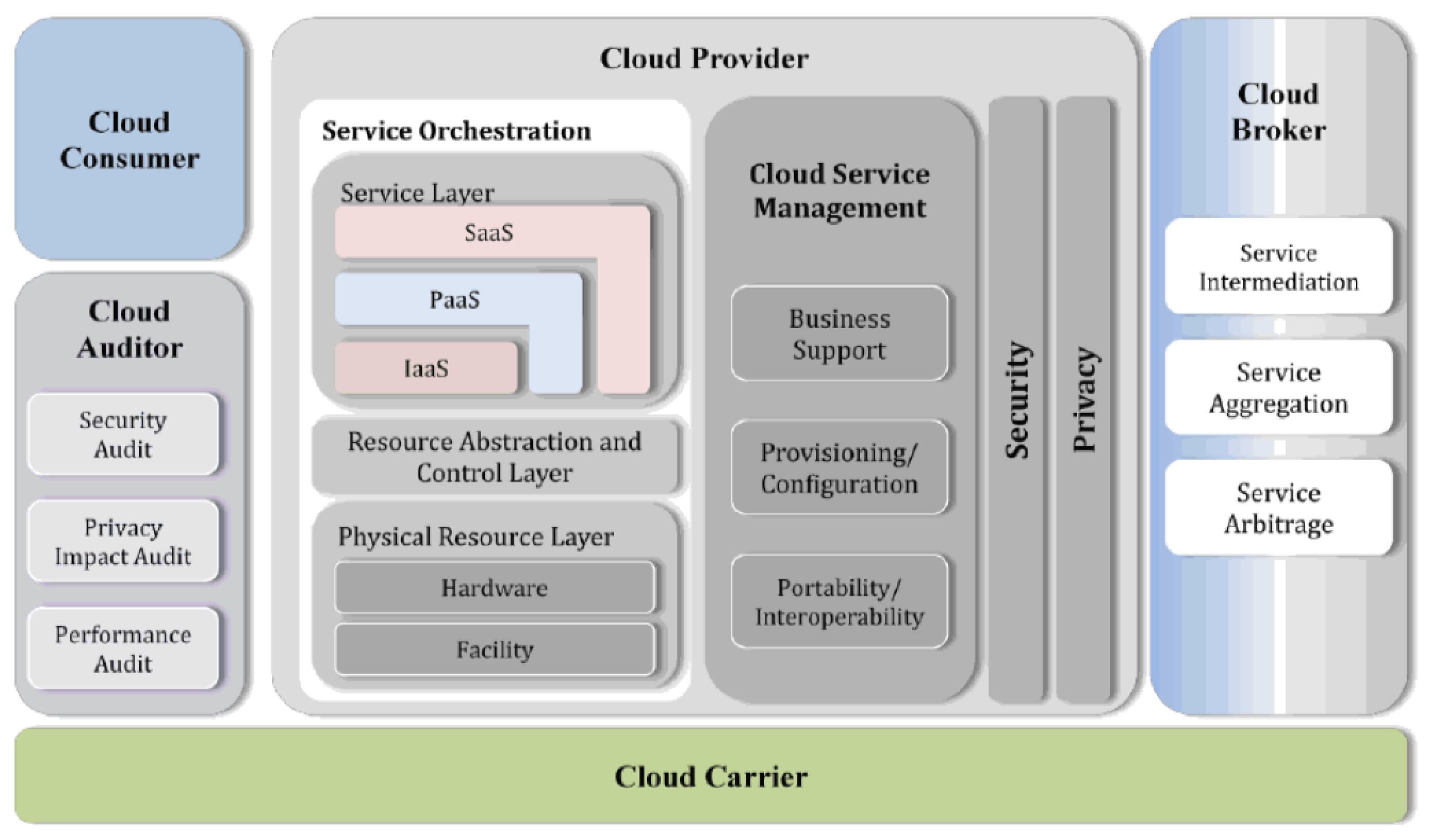
Ii provides for each cloud actor the core set of security components that fall under their.
Nist releases evaluation of cloud computing services based on nist sp 800 145 nist sp 500 322 a report that provides clarification for 1 qualifying a given nist announces 2018 small business innovation research funding opportunity.
The purpose of this document is to define a nist cloud computing security reference architecture ncc sra a framework that.
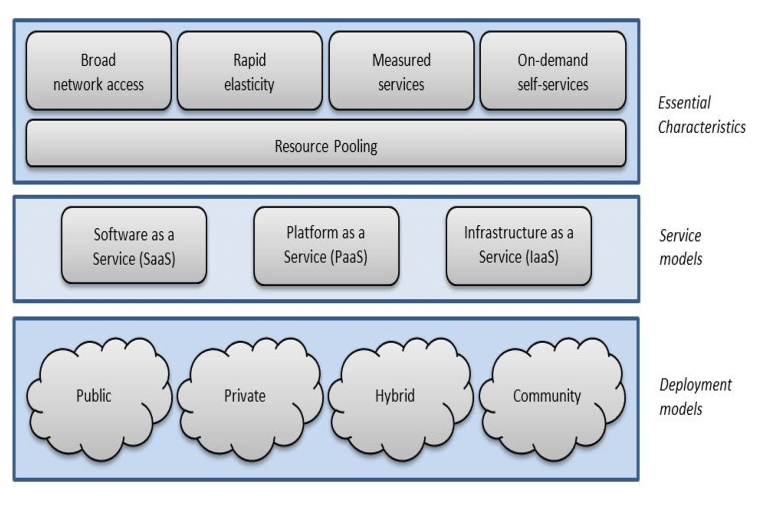
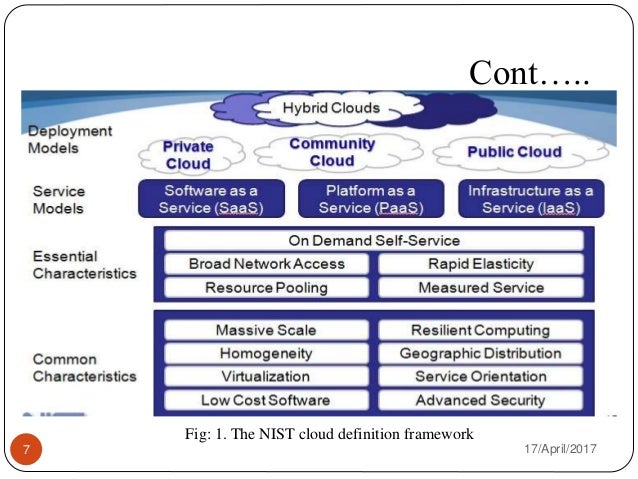
The common characteristics most interpretations share are on demand scalability of highly available and reliable pooled computing resources secure access to metered services from nearly anywhere and displacement of data and services from inside to outside the organization.
To serve as a leading communications research lab enhancing.
Cloud computing can and does mean different things to different people.
I identifies a core set of security components that can be implemented in a cloud ecosystem to secure the environment the operations and the data migrated to the cloud.
1 office of management and budget u s.
Chief information officer federal cloud computing strategy feb.
Also we show how the implementation of these controls in the cloud systems can be continuously monitored and validated.
In addition this paper shows how the implementation of these controls in the cloud systems can be continuously monitored and validated.
Furthermore cloud systems need to be continuously monitored for any misconfigurations.
While aspects of these characteristics have been.
Abstract cloud computing is a model for enabling ubiquitous convenient on demand network access to a shared pool of configurable computing resources e g networks servers storage applications and services that can be rapidly provisioned and released with minimal management effort or service provider interaction.
Apache httpd allows remote attackers to read secret data from process memory if the limit directive can be set in a user s htaccess file or if httpd conf has certain misconfigurations aka optionsbleed.